You are implementing a read-only page that includes the following controls.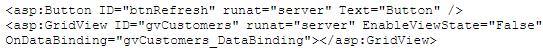
You disable view state to improve performance. You need to ensure that the page is updated to display the latest data when the user clicks the refresh button. Which code segment should you use?()
You create an ASP.NET server control in the SampleControl namespace. The control uses a JavaScript file names Refresh.js to implement AJAX functionality.You need to ensre that the JavaScript file is included in the assembly.
Which two actions should you perform?()
You are implementing a read-only page that includes the following controls.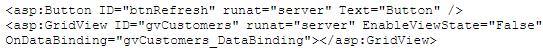
You disable view state to improve performance. You need to ensure that the page is updated to display the latest data when the user clicks the refresh button. Which code segment should you use?()
You have a Windows Server 2008 R2 Hyper-V server. You take periodic snapshots of your virtual
machines (VMs) when the VMs are not running. You delete several snapshots from the snapshot tree of a VM. The .avhd files that are associated with the deleted snapshots are not deleted from the volume where the VHD files are stored. You need to ensure that the .avhd files are deleted.
What should you do?()
You want to back up your 100-GB database on a remote tape device. You are required to ensure that minimum network bandwidth is consumed while transferring the backups to the tape device.
The current consumption of your CPU is approximately 40 percent.
Which type of backup should you perform?()
You are designing a top-level OU structure to meet the business and technical requirements.
Which top-evel OU or OUs should you use? ()
You have a computer that runs Windows 7. The computer is in a workgroup. You need to ensure that youcan decrypt Encrypting File System (EFS) files on the computer if you forget your password.
What are two possible ways to achieve this goal?()
You are responsible for implementing maintenance jobs on a SQL Server 2005 database server. Certain jobs run every Sunday and other jobs run at the beginning of every month. You need to schedule the jobs in the way that uses the least amount of administrative effort.
What should you do?()
You work as a senior administrator at ABC.com. The ABC.com network consists of a single domain named ABC.com. All servers on the ABC.com network have Windows Server 2012 R2 installed.
You are running a training exercise for junior administrators. You are currently discussing the Windows Firewall with Advanced Security feature.
Which of the following is TRUE with regards to Windows Firewall with Advanced Security?()
You are employed as the Exchange administrator at Company.com.You are in the process of
installing a new Exchange Server 2010 Organization.After the installation you send a text message to an external client and receive the subsequent non-delivery report (NDR): "Delivery has failed to these recipients or groups: [email protected] ([email protected]).The recipient’s e-mail system isn’t accepting messages now.Please try resending this message later or contact the recipient directly." You attempt to e-mail the user from an external e-mail system with great success.To ensure productivity you need to make sure e-mails can be sent to external clients from within the organization.
What should you do?()
You work in a company which uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. The instance has databases for a finance application and a manufacturing application. You want to put some limitation on the maximum CPU query time allowed by the applications, so you configure the Resource Governor to achieve this. But you notice that certain reports do not execute successfully any longer on the manufacturing application. You have to allow the manufacturing application to consume more CPU time, so you have to change the Resource Governor configuration.
Which Resource Governor component should you configure?()
Your portable computer is in sleep mode. When you resume work on the portable computer, you are not prompted for a password.
You need to ensure that you are prompted for a password each time the portable computer recovers from sleep mode.
What should you do?()
You are designing a strategy for migrating to the new environment.
Which two factions from your current environment will affect your migration strategy?()

You administer a Windows 2000 Professional computer that is shared by multiple users. You receive a phone call from one of the users of the shared computer that tells you that the computer is reporting a kernel stop error. You notice that a user has tried to install video drivers that have caused the computer to become unstable. You want to ensure that users can install only the drivers that are approved by the manufacturer.
What should you do? ()
All client computers in your network run Windows 7 Enterprise.
You need to prevent all standard user accounts from running programs that are signed by a specific publisher.
What should you do?()
You are designing a Windows 7 deployment image.
You plan to partition the hard disk of each client computer during deployment. You need to modify the unattended answer file by using a text editor.
Where should you add the disk information?()
You are working on a very large database. You had performed a binary backup of the control file a month ago. After this you added a few tablespaces, and dropped a couple of tablespaces. This morning, due to hardware failure, you lost all your control files.
How would you recover the database from this situation?()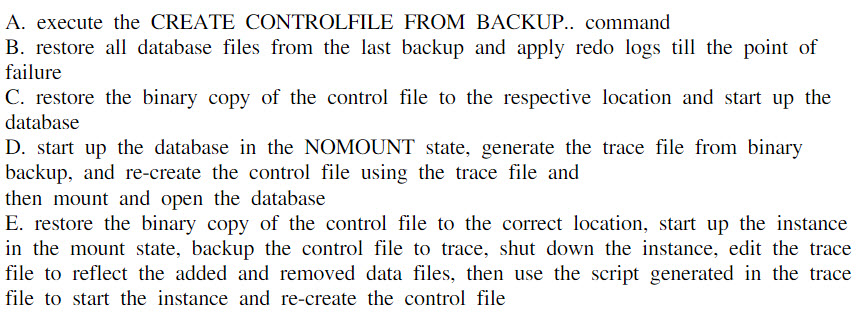
You need to identify all failed logon attempts on the domain controllers.
What should you do()
You work in a company which is named Wiikigo Corp. The company uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. There is a database named DB1 in the instance. In the database, a small percentage of data is modified everyday. Ever day in the morning, you have to create a read-only copy of the database for reporting purposes and make sure that you use as little disk space as possible.
In the options below, which strategy should you use?()
You are designing an automated deployment process for a Windows Azure application.
The process must deploy the application to Windows Azure without any user interaction. You need to recommend a deployment strategy.
What should you recommend?()
You are planning a Windows 7 deployment infrastructure for a new company.
You have the following requirements:
Three domains
10,000 client computers No user interaction
You need to recommend a deployment infrastructure.
What should you recommend?()
Your company has a single Active Directory Domain Services (AD DS) domain and 1,000 Windows 7 computers.
You are planning to deploy a custom application.
You need to schedule the deployment to occur outside of business hours and without user interaction.
Which deployment method should you choose?()
You are the network administrator for Company. to do an unattended installation so you create an Answer.txt file by using Setup Manager. The Answer.txt is copied to a floppy disk and you start the installation on a test computer by booting the computer with the Windows 2000 Professional CD-ROM. You insert the floppy disk after the computer starts. Although you had set the user interaction level to full unattended mode, you are prompted for all the required parameters. You want to ensure that the unattended installation upgrades the Windows 98 computers.
What should you do?()
You are the administrator of Red Lington Enterprises. You want to upgrade 125 computers from Windows NT Workstation 4.0 to Windows 2000 Professional. You create an unattend.txt file by using the setup manager.
You copy the file to a floppy disk. You then start the installation on a computer in the test lab using the Windows 2000 Professional CD-ROM. After the computer starts you insert the floppy disk. Even though you set the user interaction level to full-unattended mode you are prompted for all the configuration parameters. You want to ensure that the unattended installation does not prompt you for input.
What should you do? ()
You are the desktop administrator for your company. You are responsible for automating the deployment of Windows XP Professional to new computers in your company. You are preparing a Windows XP Professional computer, which you will use to test disk imaging. You install Windows XP Professional on the test computer and run the Sysprep utility. You use a third-party software package to create a disk image. You apply the disk image to a new computer and then restart the computer. Instead of completing the Windows XP Professional installation, the computer starts the Windows Welcome program, requiring you to enter additional setup information.
Because you will be deploying a large number of computers, you want to ensure that the disk image can be applied without additional user interaction. What should you do?()
You add an Online Responder to an Online Responder Array.
You need to ensure that the new Online Responder resolves synchronization conflicts for all members of the Array.
What should you do()
In your production database, data manipulation language (DML) operations are executed on the SALES table.You have noticed some dubious values in the SALES table during the last few days. You are able to track
users, actions taken, and the time of the action for this particular period but the changes in data are not tracked.You decide to keep track of both the old data and new data in the table along with the user information.
Whataction would you take to achieve this task()
You executed the following command to drop a user:
DROP USER scott CASCADE;
Which two statements regarding the above command are correct?()
You are responsible for increasing the security within the Company LAN. Of the following choices listed below,
which is true regarding layer 2 security and mitigation techniques? ()
You work as a network technician at Company. Your boss, Mrs., is interested in the Cisco Compatible Extensions program.
What are three features of this program? ()
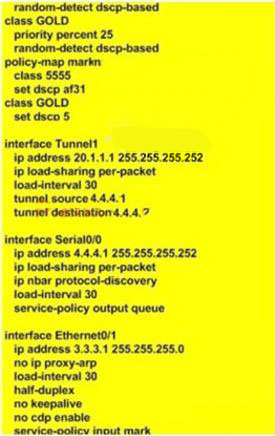
You work as a network technician at Company.com, study the exhibit provided. You are implementing this QoS configuration to improve the bandwidth guarantees for traffic towards two servers, one with the IP address 5.5.5.5 and the other with the IP address 5.5.5.4. Even after the configuration is applied, performance does not seem to improve. Which will be the most likely cause of this problem?()
You are the administrator of your company’s network. You attempt to install a printer driver on a Windows 2000 computer for a user named Linda.
You receive the following error message: "Error 11-Cannot install printer driver."
The driver was originally downloaded from the printer manufacturer’s Web site. You have successfully used the driver in the past on their Windows 2000 Professional computers.
You want to configure Linda’s computer to check for driver integrity and to allow you to install this printer driver.
What should you do? ()
根据写作要求,写出一篇作文。
You are Susan. Your company will hold an opening ceremony for a new factory. You are asked to write an invitation letter to David, an important client of your company. The following information should he included:the reasons to invite him; the time for the event;the place for the event;early reply expected.
免费的网站请分享给朋友吧