With techniques for running applications on most PC, you can ( ) a desktop icon or select the application from a menu.
Your company has an Active Directory Domain Services (AD DS) domain. You have a main office and a branch office that are connected by a slow WAN link. All servers are located in the main office.
You virtualize an application by using Microsoft Application Virtualization (App-V) 4.5. The available bandwidth is not sufficient for branch office users to run the virtualized application.
You need to ensure that branch office users can run the virtualized application by using the Microsoft Application Virtualization Desktop Client.
What should you do?()
You use Microsoft .NET Framework 4 to create a Windows application.
You want to use the ClickOnce technology to deploy the application on computers that run Windows Vista with User Access Control (UAC) enabled.
You need to ensure that the application can be installed in a secure manner.
Which setting should you use in the application manifest?()
Your company has an Active Directory Domain Services (AD DS) domain. All servers run Windows Server 2008 R2. All client computers run Windows 7. You run Remote Desktop Services and Microsoft Virtual Desktop Infrastructure (VDI). You have the serve rs shown in the following table.
You are configuring Remote Desktop Web Access (RD Web Access) to publish VDI desktops and r emote applications on the RD Web Access server.
You need to ensure that when remote users log on to the RD Web Access server they are presented with all remote applications and only their assigned VDI desktop.
Which two actions should you perform on Server 4?()

You use Microsoft .NET Framework 4 to create a Windows Presentation Foundation (WPF) application.
You use the ClickOnce deployment methodology to distribute the application.
You need to store application-specific data along with read/write permissions without requiring elevated permissions for the application.
Where should you store the application data?()
An administrator has set up serverA and serverB to use the /etc/hosts.equiv file so that applications on serverA can remotely run commands on serverB.
Which command will verify if a new user from serverA is trusted on serverB?()
A client has a temporary deployment of a new static application that needs to run for a short period of time and is not going to change.
How can this deployment be achieved with a minimum of effort and time?()
( )is not the advantage of GERT (Graphical evaluation and review techniques)as compared with PERT (project evaluation and review techniques).
A customer is running Microsoft Windows 2003, Sun Solaris, and IBM AIX with a total capacity of20 TB. This customer needs high availability for e-business applications. The servers are currently connected to two EMC Symmetrix subsystems that are running RAID 1. The customer wants to consolidate all storage into an IBM System Storage DS8700.
How many Fibre Channel drive sets are needed to satisfy the total capacity for this customer?()
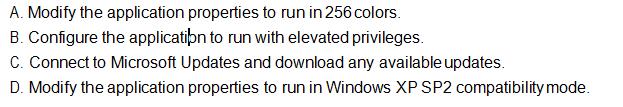
You perform an in-place upgrade on a Microsoft Windows XP Service Pack 2 (SP2) computer to Windows Vista.
After the upgrade, you attempt to run a custom application. You receive the following error message: “This application is only designed to run on Windows XP or later.”
You need to run the application on Windows Vista.
What should you do?()
An administrator wants to test the performance of an application at different memory sizes.
What is the most effective way to perform the test and collect statistical information for each test?()
Your company has a main office and four branch offices.
You have an Active Directory Domain Services (AD DS) domain. All servers run Windows Server 2008 R2.All client computers run Windows 7. You virtualize applications by using Microsoft Application Virtualization (App-V).
You need to ensure that all users access virtualized applications from their local branch office, and allow for active upgrades.
Which should you install in each branch office?()
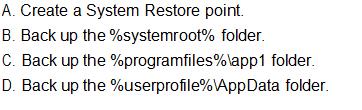
You install a custom application on a computer that runs Microsoft Windows XP. The application stores each user’s data in the %programfiles%\app1\data folder on the computer. You install the custom application on a computer that runs Windows Vista.
On the Windows Vista computer, you back up the %programfiles%\app1\data folder and notice that the backup contains no data.
You need to back up the application’s user data on the Windows Vista computer.
What should you do?()
A company needs additional storage for a block I/O based database application. The application has low I/O bandwidth requirements across the campus. The customer has a TCP/IP infrastructure and is interested in low-cost products that are compatible with its environment.
Which technology is most appropriate for this customer?()
All client computers in your company run Windows 7 Enterprise.
You are planning to deploy a custom application that runs only on Windows XP to all users.
You install Windows XP Mode on each host computer and install the application in the Windows XP guest virtual machine s (VM s ). You verify that the application runs in the guest VM s .
An a pplication shortcut does not appear on the Windows 7 host computers .
You need to ensure that the application can be launched directly from the Windows 7 host computers .
What should you do in the guest VM s ? ()
All client computers in your environment run Windows 7. You virtualize applications by using Microsoft Application Virtualization (App-V).
You need to reset the FileSystem cache on a client computer.
What should you do?()
免费的网站请分享给朋友吧