You work as the exchange administrator at TestKing.com. The TestKing.com network contains anExchange Server 2010 Organization that contains a number of Hub Transport servers.
During the course of day you receive an instruction form management to recommend a messaging
hygiene solution. Your recommendation should ensure that servers known to send spam is blocked andthat the administrative efforts are reduced.
What should you do?()
Exhibit, error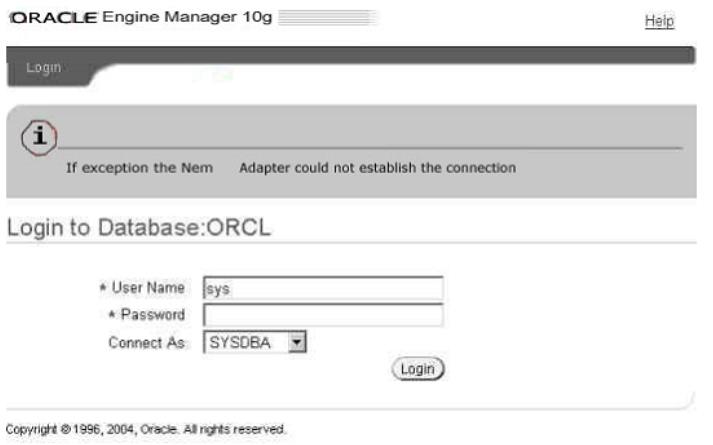
You work as a database administrator for Supportcenter.cn. When you try to connect to the database, you get an error (See exhibit). What could be the possible reason for getting such an error?()
You are the desktop administrator for ExamSheet.
Your Windows 2000 Professional computer is configured to support two monitors. You install a DOS-based application on your computer. The application uses the Windows 2000 Professional default settings Autoexec.nt and Config.nt.
Your primary video adapter is set to 24 bit color, 800 x 600 resolution, and default refresh rates. Your secondary video adapter is set to 32 bit color, 1024 x 768 resolution, and a refresh refresh of 72 hertz. You create a shortcut for the DOS-based application on the secondary monitor's desktop and use the
default PIF settings. You attempt to run the DOS-based application on the secondary monitor. The application opens, but the display area is scrambled. You then attempt to run the DOS-based application on the primary monitor.
The application does not open. Both monitors function correctly when you run Windows based applications.
You want to be able to run the DOS-based application on either monitor.
What should you do?()
You have a Windows Server 2008 R2 Hyper-V server. You take periodic snapshots of your virtual
machines (VMs) when the VMs are not running. You delete several snapshots from the snapshot tree of a VM. The .avhd files that are associated with the deleted snapshots are not deleted from the volume where the VHD files are stored. You need to ensure that the .avhd files are deleted.
What should you do?()
You work as a Web Developer at Certkiller.com. You are in the process of creating a Webapplication using Microsoft ASP.NET 3.5.
You host the Web application in Microsoft Internet Information Services (IIS) 6.0. You browse theapplication and receive the following error message:
Server Application Unavailable
The web application you are attempting to access on this web server is currently unavailable.Please hit the "Refresh" button in your web browser to retry your request.
You view the Application event log and discover the following message:
It is not possible to run two different versions of ASP.NET in the same IIS process. Please use theIIS Administration Tool to reconfigure your server to run the application in a separate process.
To ensure productivity you need to solve this problem as quick as possible.
What should you do?()
You are designing a top-level OU structure to meet the business and technical requirements.
Which top-evel OU or OUs should you use? ()
You work as a senior administrator at ABC.com. The ABC.com network consists of a single domain named ABC.com. All servers on the ABC.com network have Windows Server 2012 R2 installed, and all workstations have Windows 8 installed. You are running a training exercise for junior administrators.You are currently discussing the Always Offline Mode.
Which of the following is TRUE with regards to the Always Offline Mode?()
You work as a senior administrator at ABC.com. The ABC.com network consists of a single domain named ABC.com. All servers on the ABC.com network have Windows Server 2012 R2 installed.
You are running a training exercise for junior administrators. You are currently discussing the Windows Firewall with Advanced Security feature.
Which of the following is TRUE with regards to Windows Firewall with Advanced Security?()
The network consists of two separate autonomous systems as shown below:
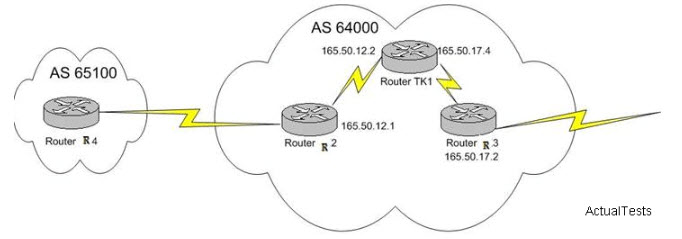
You need to configure Router R2 as a BGP route reflector and Router R1 as the client. Assumingthat Router R3 isn’t running BGP, which two of the commands below would you enter on R2 tosatisfy your goals?()
You are employed as the Exchange administrator at Company.com.You are in the process of
installing a new Exchange Server 2010 Organization.After the installation you send a text message to an external client and receive the subsequent non-delivery report (NDR): "Delivery has failed to these recipients or groups: [email protected] ([email protected]).The recipient’s e-mail system isn’t accepting messages now.Please try resending this message later or contact the recipient directly." You attempt to e-mail the user from an external e-mail system with great success.To ensure productivity you need to make sure e-mails can be sent to external clients from within the organization.
What should you do?()
You work in a company which uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. The instance has databases for a finance application and a manufacturing application. You want to put some limitation on the maximum CPU query time allowed by the applications, so you configure the Resource Governor to achieve this. But you notice that certain reports do not execute successfully any longer on the manufacturing application. You have to allow the manufacturing application to consume more CPU time, so you have to change the Resource Governor configuration.
Which Resource Governor component should you configure?()
You are a professional level SQL Server 2005 database administrator in an international corporation named Wiikigo. You are experienced in implementing high-availability solutions, monitoring the database server, and design deployment. In the company, you major job is the deployment, maintenance and support of Microsoft SQL Server 2005. You work as a database administrator for your company. There is a database named Inventory on a SQL Server 2005 computer, and the computer is named SQL01. SQL01 is utilized to aggregate manufacturing part numbers from your company’s trading partners. And the company stores the manufacturing part numbers in the Product table in the Inventory database. The company requests the users to deliver data as text files from each trading partner to SQL1 every night. The data should be imported, and no duplicate manufacturing part numbers should exist in the data which is imported from the text files, and the text files are stored in the Inventory database on SQL01. You should cut the effect on your company’s trading partners and your IT department to the least.
Which action should you perform?()
Your portable computer is in sleep mode. When you resume work on the portable computer, you are not prompted for a password.
You need to ensure that you are prompted for a password each time the portable computer recovers from sleep mode.
What should you do?()

You are designing a Windows 7 deployment image.
You plan to partition the hard disk of each client computer during deployment. You need to modify the unattended answer file by using a text editor.
Where should you add the disk information?()
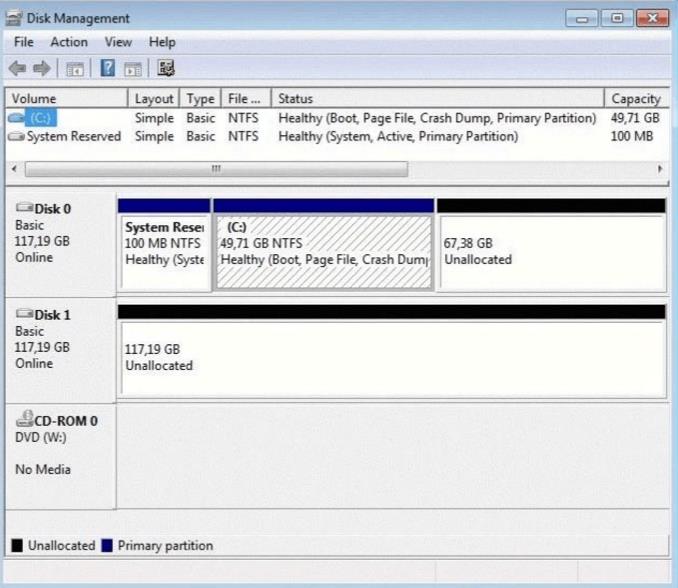
You have a computer that runs Windows 7. Your computer s disk configuration is shown in the exhibit.(Click the Exhibit button.) You need to ensure that you can create a striped volume on the computer.
What should you do?()
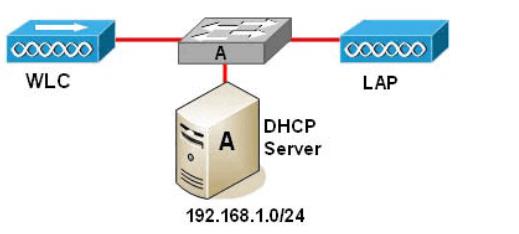
You work as a network technician at Company. Please study the exhibit carefully. In this
Company wireless network, the LAP (lightweight access point) attempts to register to a WLC (Wireless LAN Controller).
What kind of message is transmitted?()
You are working on a very large database. You had performed a binary backup of the control file a month ago. After this you added a few tablespaces, and dropped a couple of tablespaces. This morning, due to hardware failure, you lost all your control files.
How would you recover the database from this situation?()
You need to identify all failed logon attempts on the domain controllers.
What should you do()
You work in a company which is named Wiikigo Corp. The company uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. There is a database named DB1 in the instance. In the database, a small percentage of data is modified everyday. Ever day in the morning, you have to create a read-only copy of the database for reporting purposes and make sure that you use as little disk space as possible.
In the options below, which strategy should you use?()
You work in a company which is named Wiikigo Corp. The company uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. There is a text file which is named SQL01.log on the E: drive. A SQL Server Agent job executes every 2 minutes and logs information to the text file. You get a report from users saying that the sever doesn't make response. As the technical support, you check and find that the SQL Server Agent service does not run and the SQL Server Agent job no longer functions. You have to identify the reason why the SQL Server Agent service is unresponsive.
In the options below, which log should you check? ()
A co-worker is unable to invite you to a Microsoft Windows Meeting Space meeting. You need to receive an invite to the meeting.
What should you do?()
You are planning a Windows 7 deployment infrastructure for a new company.
You have the following requirements:
Three domains
10,000 client computers No user interaction
You need to recommend a deployment infrastructure.
What should you recommend?()
You are the administrator of Red Lington Enterprises. You want to upgrade 125 computers from Windows NT Workstation 4.0 to Windows 2000 Professional. You create an unattend.txt file by using the setup manager.
You copy the file to a floppy disk. You then start the installation on a computer in the test lab using the Windows 2000 Professional CD-ROM. After the computer starts you insert the floppy disk. Even though you set the user interaction level to full-unattended mode you are prompted for all the configuration parameters. You want to ensure that the unattended installation does not prompt you for input.
What should you do? ()

You work as a network engineer for . You study the exhibit carefully. Three switches are configured for HSRP. Switch1 remains in the HSRP listen state.
What is the most likely cause of this status?()
You work as the exchange administrator at TestKing.com. The TestKing.com network contains anExchange Server 2010 Organization that contains a number of Hub Transport servers.
During the course of day you receive an instruction form management to recommend a messaging
hygiene solution. Your recommendation should ensure that servers known to send spam is blocked andthat the administrative efforts are reduced.
What should you do?()
You add an Online Responder to an Online Responder Array.
You need to ensure that the new Online Responder resolves synchronization conflicts for all members of the Array.
What should you do()
You are working as a DBA on the decision support system. There is a business requirement to track and store all transactions for at least three years for a few tables in the database. Automatic undo management is enabled in the database.
Which configuration should you use to accomplish this task?()
You work as a network technician at. Your boss, Mrs. , is interested in the Spanning Tree Protocol timers.
What can you tell her regarding the default STP timers? ()
You work as a network technician at Company. Your boss, Mrs., is interested in LWAPP (Lightweight Access Point Protocol).
What should you tell her regarding this technology? ()
You work as a network technician at Company. Your boss, Mrs., is interested in the Cisco Compatible Extensions program.
What are three features of this program? ()
You are working as a Database Administrator. Despite having a password in the data dictionary as change_on_install, you always log on to the database MYNEWDB using operating system authentication. Your organization is planning to recruit two junior-level DBAs. You decide to enable remote authentication in your database so that the new DBAs can log on to the database from their workstations to carry out administrative tasks.
To allow the new DBAs to perform the administrative tasks, you create a password file on the database server using the following command:
ORAPWD file=d:\oracle\ora9i\orapwU01 password=admin entries=4
After creating the password file, you remove the operating system authentication and change the value of the REMOTE_LOGIN_PASSWORDFILE parameter to EXCLUSIVE. You also create a net service name as MYNEWDB that allows the new DBAs to connect to the database server from their workstations using this net service name. Which command must you use to connect to the database to start it?()
Exhibit:

You work as a network administrator at. You study the exhibit carefully. In the wireless LAN all devices are configured with static WEP keys.
What will happen if the access point receives packets sent by the wireless client adapter that are not encrypted with the appropriate key?()
Exhibit:
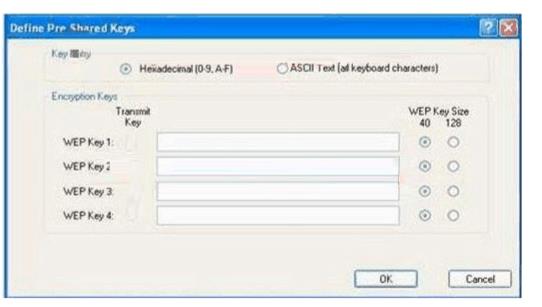
You work as a network technician at. Study the exhibit carefully. You are required configure the static WEP keys on the wireless client adapter using the Cisco ADU (Aironet Desktop Utility).
What should you have in mind when doing this?()
免费的网站请分享给朋友吧