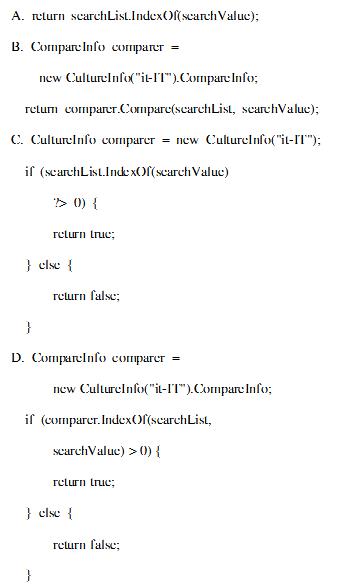
You are developing a method that searches a string for a substring. The method will be localized to Italy. Your method accepts the following parameters:
The string to be searched, which is named searchList
The string for which to search, which is named searchValue You need to write the code.
Which code segment should you use?()
You want to back up your 100-GB database on a remote tape device. You are required to ensure that minimum network bandwidth is consumed while transferring the backups to the tape device.
The current consumption of your CPU is approximately 40 percent.
Which type of backup should you perform?()
You are designing a top-level OU structure to meet the business and technical requirements.
Which top-evel OU or OUs should you use? ()
You have a computer that runs Windows 7. The computer is in a workgroup. You need to ensure that youcan decrypt Encrypting File System (EFS) files on the computer if you forget your password.
What are two possible ways to achieve this goal?()
You have a single Active Directory directory service forest with one domain. You have an existing top-level organizational unit (OU) named Sales. You are planning to create a new top-level OU named Training. The Sales and Training OUs must have the same security and auditing settings. You need to identify the security permissions and audit settings for the Sales OU so that you can delegate the same permissions for the Training OU.
What should you do first?()
You are the administrator of a Windows XP Professional computer named Pro1. The computer is connected to the Internet. Pro1 provides Internet access to eight other Windows XP Professional computers that are connected to Pro1. You enable Internet Connection Sharing (ICS) and Internet Connection Firewall (ICF) on Pro1. You run an application named App1 on Pro1. App1 communicates with an online training company on the Internet. In order to display an online seminar, the training company needs to contact the App1 application at port 5800. You want to ensure that the training company can connect to the App1 application.
What should you do?()
You are developing a method that searches a string for a substring. The method will be localized to Italy. Your method accepts the following parameters:
The string to be searched, which is named searchList
The string for which to search, which is named searchValue You need to write the code.
Which code segment should you use?()
You are employed as the Exchange administrator at Company.com.You are in the process of
installing a new Exchange Server 2010 Organization.After the installation you send a text message to an external client and receive the subsequent non-delivery report (NDR): "Delivery has failed to these recipients or groups: [email protected] ([email protected]).The recipient’s e-mail system isn’t accepting messages now.Please try resending this message later or contact the recipient directly." You attempt to e-mail the user from an external e-mail system with great success.To ensure productivity you need to make sure e-mails can be sent to external clients from within the organization.
What should you do?()
You are the administrator of Etechsol.com Enterprises. Your company consists of a small 20-user network. Management has decided to upgrade all computers to Windows 2000.
After having a closer examination of your company’s network, you realize that only half of the network interface cards are Net PC compliant. You decide to create Windows 2000 remote boot floppies.
What executable is used for creating RIS boot disks for non-PXE compliant clients?()
You work in a company which uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. The instance has databases for a finance application and a manufacturing application. You want to put some limitation on the maximum CPU query time allowed by the applications, so you configure the Resource Governor to achieve this. But you notice that certain reports do not execute successfully any longer on the manufacturing application. You have to allow the manufacturing application to consume more CPU time, so you have to change the Resource Governor configuration.
Which Resource Governor component should you configure?()
Your portable computer is in sleep mode. When you resume work on the portable computer, you are not prompted for a password.
You need to ensure that you are prompted for a password each time the portable computer recovers from sleep mode.
What should you do?()
You have a portable computer that runs Windows XP Professional. The computer supports Advanced Configuration and Power Interface (ACPI). You need to ensure that the computer enters Sleep Mode when you close the lid of the computer.
What should you do?()
You are designing a strategy for migrating to the new environment.
Which two factions from your current environment will affect your migration strategy?()

All client computers in your network run Windows 7 Enterprise.
You need to prevent all standard user accounts from running programs that are signed by a specific publisher.
What should you do?()
You are designing a Windows 7 deployment image.
You plan to partition the hard disk of each client computer during deployment. You need to modify the unattended answer file by using a text editor.
Where should you add the disk information?()
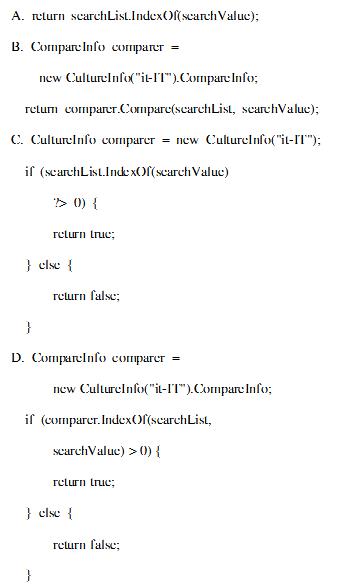
You have a computer that runs Windows 7. Your computer s disk configuration is shown in the exhibit.(Click the Exhibit button.) You need to ensure that you can create a striped volume on the computer.
What should you do?()
You work in a company which is named Wiikigo Corp. The company uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. There is a database named DB1 in the instance. In the database, a small percentage of data is modified everyday. Ever day in the morning, you have to create a read-only copy of the database for reporting purposes and make sure that you use as little disk space as possible.
In the options below, which strategy should you use?()
You are designing an automated deployment process for a Windows Azure application.
The process must deploy the application to Windows Azure without any user interaction. You need to recommend a deployment strategy.
What should you recommend?()
You are planning a Windows 7 deployment infrastructure for a new company.
You have the following requirements:
Three domains
10,000 client computers No user interaction
You need to recommend a deployment infrastructure.
What should you recommend?()
Your company has a single Active Directory Domain Services (AD DS) domain and 1,000 Windows 7 computers.
You are planning to deploy a custom application.
You need to schedule the deployment to occur outside of business hours and without user interaction.
Which deployment method should you choose?()
You are the network administrator for Company. to do an unattended installation so you create an Answer.txt file by using Setup Manager. The Answer.txt is copied to a floppy disk and you start the installation on a test computer by booting the computer with the Windows 2000 Professional CD-ROM. You insert the floppy disk after the computer starts. Although you had set the user interaction level to full unattended mode, you are prompted for all the required parameters. You want to ensure that the unattended installation upgrades the Windows 98 computers.
What should you do?()
You are the administrator of Red Lington Enterprises. You want to upgrade 125 computers from Windows NT Workstation 4.0 to Windows 2000 Professional. You create an unattend.txt file by using the setup manager.
You copy the file to a floppy disk. You then start the installation on a computer in the test lab using the Windows 2000 Professional CD-ROM. After the computer starts you insert the floppy disk. Even though you set the user interaction level to full-unattended mode you are prompted for all the configuration parameters. You want to ensure that the unattended installation does not prompt you for input.
What should you do? ()
You are the desktop administrator for your company. You are responsible for automating the deployment of Windows XP Professional to new computers in your company. You are preparing a Windows XP Professional computer, which you will use to test disk imaging. You install Windows XP Professional on the test computer and run the Sysprep utility. You use a third-party software package to create a disk image. You apply the disk image to a new computer and then restart the computer. Instead of completing the Windows XP Professional installation, the computer starts the Windows Welcome program, requiring you to enter additional setup information.
Because you will be deploying a large number of computers, you want to ensure that the disk image can be applied without additional user interaction. What should you do?()

You work as a network engineer for . You study the exhibit carefully. Three switches are configured for HSRP. Switch1 remains in the HSRP listen state.
What is the most likely cause of this status?()
You add an Online Responder to an Online Responder Array. You need to ensure that the new Online Responder resolves synchronization conflicts for all members of the Array.
What should you do()
You are working as a DBA on the decision support system. There is a business requirement to track and store all transactions for at least three years for a few tables in the database. Automatic undo management is enabled in the database.
Which configuration should you use to accomplish this task?()
You have a computer that runs Windows XP Professional. You download new video card driver from the Internet, and then install the driver. You restart the computer. You discover that the newly loaded video driver is named VgaSave.
You need to restore the previous version of the video card driver.What should you do?()
You are the newly appointed system administrator at Certkiller.com. You are in the process ofcreating a Microsoft ASP.NET application using Microsoft .NET Framework v3.5.
The new application will make use of eleven themes. Certkiller clients will be permitted to selecttheir themes from the Web page. You need to make sure that the theme selected by a client isdisplayed when the client returns to the application. This should occur even when the client returnsto log on at a later date or from another workstation.
You should take cognizance of the fact that the application operates on different storage types andin different environments. Management wants you tp store the themes selected by the clients aswell as retrieving the required theme.
What should you do?()
You plan to deploy a Virtual Desktop Infrastructure (VDI) for the public relations users.
You need to identify which additional software must be deployed on the network to support the planned VDI deployment.
Which additional software should you identify?()
You have an enterprise subordinate certification authority (CA) configured for key archival. Three key recovery agent certificates are issued. The CA is configured to use two recovery agents.
You need to ensure that all of the recovery agent certificates can be used to recover all new private keys.
What should you do()
根据写作要求,写出一篇作文。
You are Susan. Your company will hold an opening ceremony for a new factory. You are asked to write an invitation letter to David, an important client of your company. The following information should he included:the reasons to invite him; the time for the event;the place for the event;early reply expected.
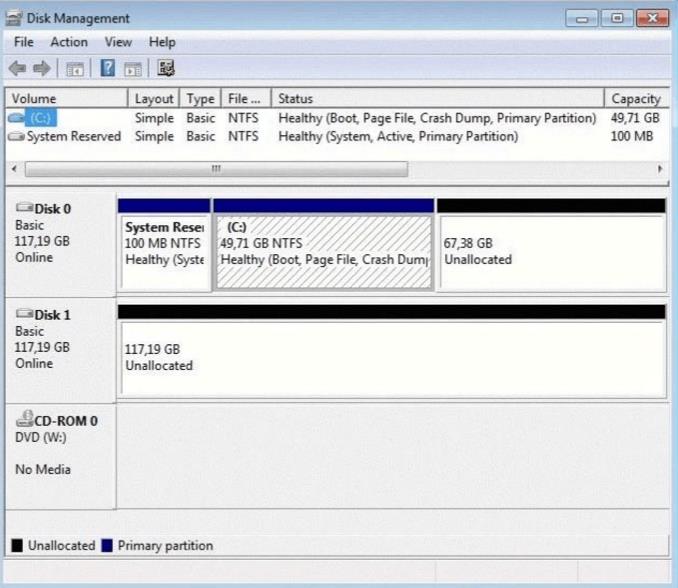
You are implementing a read-only page that includes the following controls.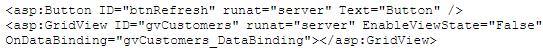
You disable view state to improve performance. You need to ensure that the page is updated to display the latest data when the user clicks the refresh button. Which code segment should you use?()
You have a Windows Server 2008 R2 Hyper-V server. You take periodic snapshots of your virtual
machines (VMs) when the VMs are not running. You delete several snapshots from the snapshot tree of a VM. The .avhd files that are associated with the deleted snapshots are not deleted from the volume where the VHD files are stored. You need to ensure that the .avhd files are deleted.
What should you do?()
免费的网站请分享给朋友吧