All client computers in your network run Windows 7 Enterprise.
You need to prevent all standard user accounts from running programs that are signed by a specific publisher.
What should you do?()
Your network includes the servers shown in the following table:
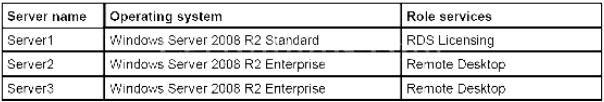
Per-device Remote Desktop Services client access licenses (RDS CALs) are installed on Server1. After you refresh a group of client computers with Windows 7, users on those computers can no longer connect to Server2. You need to ensure that the users can connect to remote applications.
What should you do?()
Your network includes the servers shown in the following table. Server n ame Operating s ystem Role s ervices S erver 1 Windows Server 2008 R2 Standard RDS Licensing S erver 2 Windows Server 2008 R2 Enterprise Remote Desktop Server3 Windows Server 2008 R2 Enterprise Remote Desktop Per-device Remote Desktop Services client access licenses (RDS CALs) are installed on Server1. After you refresh a group of client computers with Windows 7, users on those computers can no longer connect to Server2. You need to ensure that the users can connect to remote applications.
What should you do?()
You are the network administrator for the Paris branch office of Fourth Coffee.The Paris office has a Windows Server 2003 DNS server named Server10. Server10 hosts a DNS primary zone named fourthcoffee.com. All computers in the Paris office are configured to use Server10 as their preferred DNS server. The Berlin branch office of Fourth Coffee has a UNIX DNS server named Server11. Server11 hosts a primary zone named engineering.fourthcoffee.com. The refresh interval of the engineering.fourthcoffee.com zone is set to 24 hours. In the Berlin office, a firewall filters all incoming network traffic from other offices. A rule on this firewall prevents all computers from the Paris office network, except Server10, from performing DNS lookups against Server11.There is a business requirement that no delay should occur between the time that a new record is created in the engineering.fourthcoffee.com zone and the time that the record can be resolved from any computers in the Paris office. All computers in the Paris office must be able to resolve names in the engineering.fourthcoffee.com namespace.You need to configure DNS on Server10 to meet the requirements.
What should you do?()
You are a network administrator for Litware, Inc. The company’s main office is located in Lima, and branch offices are located in five other cities. The network consists of a single DNS domain named litwareinc.com. The network configuration is shown in the exhibit. (Click the Exhibit button.)
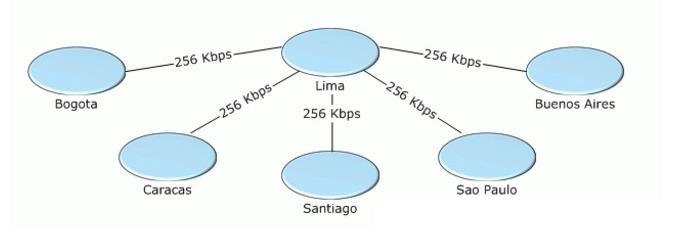
All network servers run Windows Server 2003. All client computer IP addresses are assigned by using a DHCP server that is located in each office. Client computers are reimaged often and are assigned new names each time they are reimaged. All client computers are configured to reference their local DNS server as the preferred DNS server and to reference the central DNS server as the alternate DNS server.A primary zone for litwareinc.com is configured on a server in the Lima office. Secondary zones are configured on a server in each branch office. The retry interval, the refresh interval, the expiration interval, and the default minimum Time to Live (TTL) interval are configured with the default settings.Network bandwidth utilization averages 40 percent. The network connection between the Lima office and the Bogota office fails an average of twice per day.Users in the Bogota office occasionally receive incorrect responses to queries against the local DNS server when the network connection is interrupted during a zone transfer.
You need to change the configuration of the start of authority (SOA) resource record for litwareinc.com. In addition, you need to reduce the possibility that users can query local DNS zones before successful zone transfers occur.
What should you do?()
You are designing a top-level OU structure to meet the business and technical requirements.
Which top-evel OU or OUs should you use? ()
You have a computer that runs Windows 7. The computer is in a workgroup. You need to ensure that youcan decrypt Encrypting File System (EFS) files on the computer if you forget your password.
What are two possible ways to achieve this goal?()
You are employed as the Exchange administrator at Company.com.You are in the process of
installing a new Exchange Server 2010 Organization.After the installation you send a text message to an external client and receive the subsequent non-delivery report (NDR): "Delivery has failed to these recipients or groups: [email protected] ([email protected]).The recipient’s e-mail system isn’t accepting messages now.Please try resending this message later or contact the recipient directly." You attempt to e-mail the user from an external e-mail system with great success.To ensure productivity you need to make sure e-mails can be sent to external clients from within the organization.
What should you do?()
You are the administrator of Etechsol.com Enterprises. Your company consists of a small 20-user network. Management has decided to upgrade all computers to Windows 2000.
After having a closer examination of your company’s network, you realize that only half of the network interface cards are Net PC compliant. You decide to create Windows 2000 remote boot floppies.
What executable is used for creating RIS boot disks for non-PXE compliant clients?()
You have two computers named Computer1 and Computer2 that run Windows 7. Computer1 has two localuser accounts named User1 and User2. On Computer1, you run Scanstate.exe /all \\server1\data \computer1. On Computer2, you run Loadstate.exe /lac:Pa$$w0rd \\server1\data\computer1. You need toensure that User1 and User2 can log on to Computer2.
What should you do on Computer2?()
You have a portable computer that runs Windows 7. You configure the computer to enter sleep mode after10 minutes of inactivity. You do not use the computer for 15 minutes and discover that the computer has notentered sleep mode. You need to identify what is preventing the computer from entering sleep mode.
What should you do?()
Your portable computer is in sleep mode. When you resume work on the portable computer, you are not prompted for a password.
You need to ensure that you are prompted for a password each time the portable computer recovers from sleep mode.
What should you do?()
You have a portable computer that runs Windows XP Professional. The computer supports Advanced Configuration and Power Interface (ACPI). You need to ensure that the computer enters Sleep Mode when you close the lid of the computer.
What should you do?()

You administer a Windows 2000 Professional computer that is shared by multiple users. You receive a phone call from one of the users of the shared computer that tells you that the computer is reporting a kernel stop error. You notice that a user has tried to install video drivers that have caused the computer to become unstable. You want to ensure that users can install only the drivers that are approved by the manufacturer.
What should you do? ()
All client computers in your network run Windows 7 Enterprise.
You need to prevent all standard user accounts from running programs that are signed by a specific publisher.
What should you do?()
You are designing a Windows 7 deployment image.
You plan to partition the hard disk of each client computer during deployment. You need to modify the unattended answer file by using a text editor.
Where should you add the disk information?()
You have a server named Server1 that runs Windows Server 2003 Service Pack 2 (SP2).
Server1 runs an application named App1. All client computers run Windows XP Professional Service Pack 3 (SP3). Users from a remote network segment report poor performance when they run App1. You need to identify whether the cause of the poor network performance is packet loss.
Which tool should you use?()
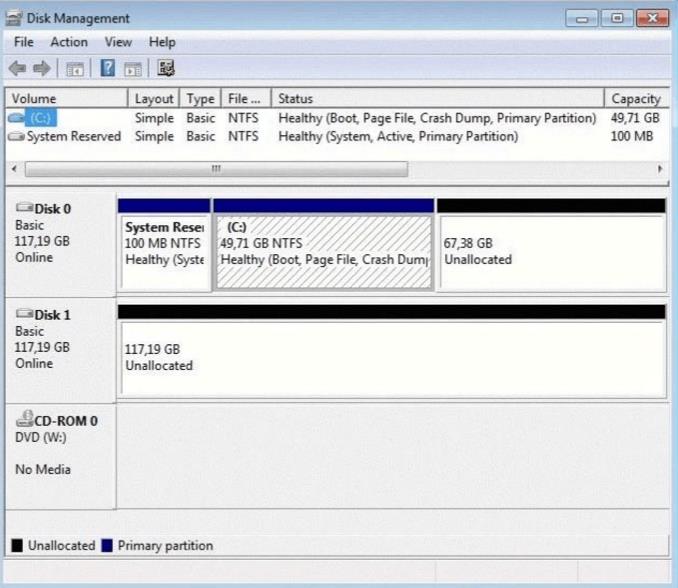
You have a computer that runs Windows 7. Your computer s disk configuration is shown in the exhibit.(Click the Exhibit button.) You need to ensure that you can create a striped volume on the computer.
What should you do?()
You need to identify all failed logon attempts on the domain controllers.
What should you do()
You need to design a Windows Server Update Services (WSUS) infrastructure that meets the following requirements:
èThe updates must be distributed from a central location.
èAll computers must continue to receive updates in the event that a server fails.
What should you include in your design?()
Your network contains several Windows Server 2008 R2 servers that run Windows Server Update
Services (WSUS). The WSUS servers distribute updates to all computers on the internal network. Remote users connect from their personal computers to the internal network by using a split-tunnel VPN connection.
You need to plan a strategy for patch management that deploys updates on the remote users coputers.
Your strategy must meet the following requirements:
èMinimize bandwidth use over the VPN connections.
èRequire updates to be approved on the WSUS servers before they are installed on the client computers.
What should you include in your plan?()
You are building a dating web site. The client’s date of birth is collected along with lots of other information.You have created an EL function with the signature:
calcAge(java.util.Date):int and it is assigned to the name, age, in the namespace, funct. In one of your JSPsyou need to print a special message to clients who are younger than 25.
Which EL code snippet will returntrue for this condition?()
You are planning a Windows 7 deployment infrastructure for a new company.
You have the following requirements:
Three domains
10,000 client computers No user interaction
You need to recommend a deployment infrastructure.
What should you recommend?()
You are the network administrator for Company. to do an unattended installation so you create an Answer.txt file by using Setup Manager. The Answer.txt is copied to a floppy disk and you start the installation on a test computer by booting the computer with the Windows 2000 Professional CD-ROM. You insert the floppy disk after the computer starts. Although you had set the user interaction level to full unattended mode, you are prompted for all the required parameters. You want to ensure that the unattended installation upgrades the Windows 98 computers.
What should you do?()
You are the administrator of Red Lington Enterprises. You want to upgrade 125 computers from Windows NT Workstation 4.0 to Windows 2000 Professional. You create an unattend.txt file by using the setup manager.
You copy the file to a floppy disk. You then start the installation on a computer in the test lab using the Windows 2000 Professional CD-ROM. After the computer starts you insert the floppy disk. Even though you set the user interaction level to full-unattended mode you are prompted for all the configuration parameters. You want to ensure that the unattended installation does not prompt you for input.
What should you do? ()
You are the desktop administrator for your company. You are responsible for automating the deployment of Windows XP Professional to new computers in your company. You are preparing a Windows XP Professional computer, which you will use to test disk imaging. You install Windows XP Professional on the test computer and run the Sysprep utility. You use a third-party software package to create a disk image. You apply the disk image to a new computer and then restart the computer. Instead of completing the Windows XP Professional installation, the computer starts the Windows Welcome program, requiring you to enter additional setup information.
Because you will be deploying a large number of computers, you want to ensure that the disk image can be applied without additional user interaction. What should you do?()
You are the administrator of a Microsoft Windows Server 2003 computer named Server1. SQL Server 2005 is installed on Server1 to host a database named MedDB. The MedDB database serves as the backend database for a new client/server application named MedDATA. Installation of the MedDATA application creates the database schema, application roles, and administrative accounts. It also sets all of the default permissions. You need to establish a permissions baseline for all objects in the MedDB database.
What should you do?()
You have a computer that runs Windows XP Professional. Two users named User1 and User2 share the computer. User1 and User2 encrypt files on the computer. User1 encrypts a file named file1. doc. You need ensure that both User1 and User2 can view the contents of file1. doc.
What should you instruct User1 to do?()
You have a computer that runs Windows XP Professional. You download new video card driver from the Internet, and then install the driver. You restart the computer. You discover that the newly loaded video driver is named VgaSave.
You need to restore the previous version of the video card driver.What should you do?()
You are the administrator of your company’s network. You attempt to install a printer driver on a Windows 2000 computer for a user named Linda.
You receive the following error message: "Error 11-Cannot install printer driver."
The driver was originally downloaded from the printer manufacturer’s Web site. You have successfully used the driver in the past on their Windows 2000 Professional computers.
You want to configure Linda’s computer to check for driver integrity and to allow you to install this printer driver.
What should you do? ()
You are the administrator of ExamSheet.net's network.
You attempt to install a video driver on a Windows 2000 Professional computer. You receive the following error message: "Error 11 - Cannot install video driver."
The driver was originally downloaded from the video card manufacturer's Web site. You have successfully used the driver in the past on other Windows 2000 Professional computers. You want to configure the Windows 2000 Professional computer to check for driver integrity and to allow you to install this video driver. What should you do? ()
You are the newly appointed system administrator at Certkiller.com. You are in the process ofcreating a Microsoft ASP.NET application using Microsoft .NET Framework v3.5.
The new application will make use of eleven themes. Certkiller clients will be permitted to selecttheir themes from the Web page. You need to make sure that the theme selected by a client isdisplayed when the client returns to the application. This should occur even when the client returnsto log on at a later date or from another workstation.
You should take cognizance of the fact that the application operates on different storage types andin different environments. Management wants you tp store the themes selected by the clients aswell as retrieving the required theme.
What should you do?()
Exhibit:

You work as a network administrator at. You study the exhibit carefully. In the wireless LAN all devices are configured with static WEP keys.
What will happen if the access point receives packets sent by the wireless client adapter that are not encrypted with the appropriate key?()
免费的网站请分享给朋友吧