You are the network administrator for Contoso Pharmaceuticals. Your network consists of a single Active Directory forest that contains three domains. The forest root domain is named contoso.com. The domain contains two child domains named usa.contoso.com and europe.contoso.com. The functional level of the forest is Windows Server 2003. Each domain contains two Windows Server 2003 domain controllers named DC1 and DC2. DC1 in the contoso.com domain performs the following two operations master roles: schema master and domain naming master. DC1 in each child domain performs the following three operations master roles: PDC emulator master, relative ID (RID) master, and infrastructure master. DC1 in each domain is also a global catalog server. The user account for Nancy Buchanan in the europe.contoso.com domain is a member of the Medicine Students security group. Because of a name change, the domain administrator of europe.contoso.com changes the Last name field of Nancy's useraccount from Buchanan to Anderson. The domain administrator of usa.contoso.com discovers that the user account for Nancy is still listed as Nancy Buchanan. You need to ensure that the user account for Nancy Anderson is correctly listed in the Medicine Students group.
What should you do?()
You create Windows Forms applications by using the .NET Framework 3.5. You plan to deploy a new application by using the ClickOnce technology.During deployment, the application performs the following tasks:
(1)Modifies registry keys
(2)Modifies the files located in the %PROGRAM FILES% folder
(3)Administrative permissions are not granted to users who install the application
You need to ensure that the following requirements are met:
(1)The application can be deployed to Windows Vista client computers that are not part of an Active Directory domain
(2)When the application is deployed, users are not prompted to elevate their permissions
What should you do?()
根据写作要求,写出一篇作文。
You are Susan. Your company will hold an opening ceremony for a new factory. You are asked to write an invitation letter to David, an important client of your company. The following information should he included:the reasons to invite him; the time for the event;the place for the event;early reply expected.
You create an ASP.NET server control in the SampleControl namespace. The control uses a JavaScript file names Refresh.js to implement AJAX functionality.You need to ensre that the JavaScript file is included in the assembly.
Which two actions should you perform?()
You are implementing a read-only page that includes the following controls.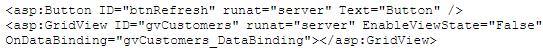
You disable view state to improve performance. You need to ensure that the page is updated to display the latest data when the user clicks the refresh button. Which code segment should you use?()
You have a Windows Server 2008 R2 Hyper-V server. You take periodic snapshots of your virtual
machines (VMs) when the VMs are not running. You delete several snapshots from the snapshot tree of a VM. The .avhd files that are associated with the deleted snapshots are not deleted from the volume where the VHD files are stored. You need to ensure that the .avhd files are deleted.
What should you do?()
You work as a Web Developer at Certkiller.com. You are in the process of creating a Webapplication using Microsoft ASP.NET 3.5.
You host the Web application in Microsoft Internet Information Services (IIS) 6.0. You browse theapplication and receive the following error message:
Server Application Unavailable
The web application you are attempting to access on this web server is currently unavailable.Please hit the "Refresh" button in your web browser to retry your request.
You view the Application event log and discover the following message:
It is not possible to run two different versions of ASP.NET in the same IIS process. Please use theIIS Administration Tool to reconfigure your server to run the application in a separate process.
To ensure productivity you need to solve this problem as quick as possible.
What should you do?()
You are designing a top-level OU structure to meet the business and technical requirements.
Which top-evel OU or OUs should you use? ()
You are responsible for implementing maintenance jobs on a SQL Server 2005 database server. Certain jobs run every Sunday and other jobs run at the beginning of every month. You need to schedule the jobs in the way that uses the least amount of administrative effort.
What should you do?()
You are employed as the Exchange administrator at Company.com.You are in the process of
installing a new Exchange Server 2010 Organization.After the installation you send a text message to an external client and receive the subsequent non-delivery report (NDR): "Delivery has failed to these recipients or groups: [email protected] ([email protected]).The recipient’s e-mail system isn’t accepting messages now.Please try resending this message later or contact the recipient directly." You attempt to e-mail the user from an external e-mail system with great success.To ensure productivity you need to make sure e-mails can be sent to external clients from within the organization.
What should you do?()
You work in a company which uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. The instance has databases for a finance application and a manufacturing application. You want to put some limitation on the maximum CPU query time allowed by the applications, so you configure the Resource Governor to achieve this. But you notice that certain reports do not execute successfully any longer on the manufacturing application. You have to allow the manufacturing application to consume more CPU time, so you have to change the Resource Governor configuration.
Which Resource Governor component should you configure?()
You are using an Automatic Storage Management (ASM) instance to manage the files of your production database. While studying the parameter file of the ASM instance, you find the following entry:
ASM_DISKSTRING = /devices/*
What could be the reason for this setting?()
Your portable computer is in sleep mode. When you resume work on the portable computer, you are not prompted for a password.
You need to ensure that you are prompted for a password each time the portable computer recovers from sleep mode.
What should you do?()

You administer a Windows 2000 Professional computer that is shared by multiple users. You receive a phone call from one of the users of the shared computer that tells you that the computer is reporting a kernel stop error. You notice that a user has tried to install video drivers that have caused the computer to become unstable. You want to ensure that users can install only the drivers that are approved by the manufacturer.
What should you do? ()
You are designing a Windows 7 deployment image.
You plan to partition the hard disk of each client computer during deployment. You need to modify the unattended answer file by using a text editor.
Where should you add the disk information?()
You create a Microsoft ASP.NET application by using the Microsoft .NET Framework version 3.5.
You create a page that contains the following code fragment.
English
Chinese
Japan
Korean
- 92 - Test Information Co., Ltd. All rights reserved. <asp:ListBox ID="lstLanguages"AutoPostBack="true" runat="server" />
You write the following code segment in the code-behind file for the page.
void BindData(object sender, EventArgs e) {
lstLanguages.DataSource =
CultureInfo.GetCultures(CultureTypes.AllCultures);
lstLanguages.DataTextField = "EnglishName";
lstLanguages.DataBind();
}
You need to ensure that the lstLanguages ListBox control maintains the selection of the user during postback.
Which line of code should you insert in the constructor of the page?()
You work in a company which is named Wiikigo Corp. The company uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. There is a database named DB1 in the instance. In the database, a small percentage of data is modified everyday. Ever day in the morning, you have to create a read-only copy of the database for reporting purposes and make sure that you use as little disk space as possible.
In the options below, which strategy should you use?()
You work in a company which is named Wiikigo Corp. The company uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. There is a text file which is named SQL01.log on the E: drive. A SQL Server Agent job executes every 2 minutes and logs information to the text file. You get a report from users saying that the sever doesn't make response. As the technical support, you check and find that the SQL Server Agent service does not run and the SQL Server Agent job no longer functions. You have to identify the reason why the SQL Server Agent service is unresponsive.
In the options below, which log should you check? ()
You are designing an automated deployment process for a Windows Azure application.
The process must deploy the application to Windows Azure without any user interaction. You need to recommend a deployment strategy.
What should you recommend?()
You are planning a Windows 7 deployment infrastructure for a new company.
You have the following requirements:
Three domains
10,000 client computers No user interaction
You need to recommend a deployment infrastructure.
What should you recommend?()
You are the network administrator for Company. to do an unattended installation so you create an Answer.txt file by using Setup Manager. The Answer.txt is copied to a floppy disk and you start the installation on a test computer by booting the computer with the Windows 2000 Professional CD-ROM. You insert the floppy disk after the computer starts. Although you had set the user interaction level to full unattended mode, you are prompted for all the required parameters. You want to ensure that the unattended installation upgrades the Windows 98 computers.
What should you do?()
You are the administrator of Red Lington Enterprises. You want to upgrade 125 computers from Windows NT Workstation 4.0 to Windows 2000 Professional. You create an unattend.txt file by using the setup manager.
You copy the file to a floppy disk. You then start the installation on a computer in the test lab using the Windows 2000 Professional CD-ROM. After the computer starts you insert the floppy disk. Even though you set the user interaction level to full-unattended mode you are prompted for all the configuration parameters. You want to ensure that the unattended installation does not prompt you for input.
What should you do? ()
You are the desktop administrator for your company. You are responsible for automating the deployment of Windows XP Professional to new computers in your company. You are preparing a Windows XP Professional computer, which you will use to test disk imaging. You install Windows XP Professional on the test computer and run the Sysprep utility. You use a third-party software package to create a disk image. You apply the disk image to a new computer and then restart the computer. Instead of completing the Windows XP Professional installation, the computer starts the Windows Welcome program, requiring you to enter additional setup information.
Because you will be deploying a large number of computers, you want to ensure that the disk image can be applied without additional user interaction. What should you do?()
In your production database, data manipulation language (DML) operations are executed on the SALES table.You have noticed some dubious values in the SALES table during the last few days. You are able to track
users, actions taken, and the time of the action for this particular period but the changes in data are not tracked.You decide to keep track of both the old data and new data in the table along with the user information.
Whataction would you take to achieve this task()
You executed the following command to drop a user:
DROP USER scott CASCADE;
Which two statements regarding the above command are correct?()
You are responsible for increasing the security within the Company LAN. Of the following choices listed below,
which is true regarding layer 2 security and mitigation techniques? ()
You have a computer that runs Windows XP Professional. You download new video card driver from the Internet, and then install the driver. You restart the computer. You discover that the newly loaded video driver is named VgaSave.
You need to restore the previous version of the video card driver.What should you do?()
You are the administrator of your company’s network. You attempt to install a printer driver on a Windows 2000 computer for a user named Linda.
You receive the following error message: "Error 11-Cannot install printer driver."
The driver was originally downloaded from the printer manufacturer’s Web site. You have successfully used the driver in the past on their Windows 2000 Professional computers.
You want to configure Linda’s computer to check for driver integrity and to allow you to install this printer driver.
What should you do? ()
You are the administrator of ExamSheet.net's network.
You attempt to install a video driver on a Windows 2000 Professional computer. You receive the following error message: "Error 11 - Cannot install video driver."
The driver was originally downloaded from the video card manufacturer's Web site. You have successfully used the driver in the past on other Windows 2000 Professional computers. You want to configure the Windows 2000 Professional computer to check for driver integrity and to allow you to install this video driver. What should you do? ()
You are the network administrator for ExamSheet.net. Your network has 210 Windows 2000 Professional computers and eleven Windows 2000 Server computers. Users on the network save their work files in home folders on a network server. The NTFS partition that contains the home folders has Encrypting File System (EFS) enabled. A user named Sandra leaves ExamSheet.net. You decrypt the files for her manager. When the manager attempts to open any of the files, he receives the following error message: "Access is denied." You want the manager to be able to access the files.
What should do? ()
You are the newly appointed system administrator at Certkiller.com. You are in the process ofcreating a Microsoft ASP.NET application using Microsoft .NET Framework v3.5.
The new application will make use of eleven themes. Certkiller clients will be permitted to selecttheir themes from the Web page. You need to make sure that the theme selected by a client isdisplayed when the client returns to the application. This should occur even when the client returnsto log on at a later date or from another workstation.
You should take cognizance of the fact that the application operates on different storage types andin different environments. Management wants you tp store the themes selected by the clients aswell as retrieving the required theme.
What should you do?()
You are working as a Database Administrator. Despite having a password in the data dictionary as change_on_install, you always log on to the database MYNEWDB using operating system authentication. Your organization is planning to recruit two junior-level DBAs. You decide to enable remote authentication in your database so that the new DBAs can log on to the database from their workstations to carry out administrative tasks.
To allow the new DBAs to perform the administrative tasks, you create a password file on the database server using the following command:
ORAPWD file=d:\oracle\ora9i\orapwU01 password=admin entries=4
After creating the password file, you remove the operating system authentication and change the value of the REMOTE_LOGIN_PASSWORDFILE parameter to EXCLUSIVE. You also create a net service name as MYNEWDB that allows the new DBAs to connect to the database server from their workstations using this net service name. Which command must you use to connect to the database to start it?()
Exhibit:

You work as a network administrator at. You study the exhibit carefully. In the wireless LAN all devices are configured with static WEP keys.
What will happen if the access point receives packets sent by the wireless client adapter that are not encrypted with the appropriate key?()
免费的网站请分享给朋友吧