You have very few Cisco 7920 wireless IP phones on your network, but lots of wireless laptops. Youwant to increase the bandwidth available for the laptops by decreasing the bandwidth reserved forthe Cisco 7920 phones.
What is the lowest percentage of voice-allocated bandwidth you can select onthe WLAN controller?()
Exhibit:
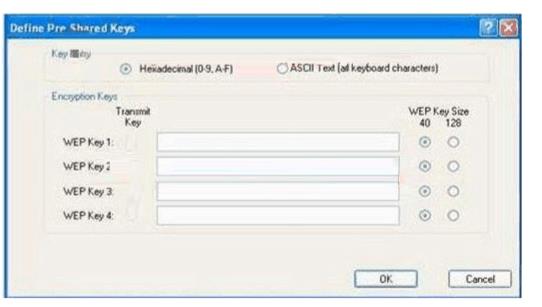
You work as a network technician at. Study the exhibit carefully. You are required configure the static WEP keys on the wireless client adapter using the Cisco ADU (Aironet Desktop Utility).
What should you have in mind when doing this?()
You have an enterprise subordinate certification authority (CA) configured for key archival. Three key recovery agent certificates are issued. The CA is configured to use two recovery agents.
You need to ensure that all of the recovery agent certificates can be used to recover all new private keys.
What should you do()
You have an enterprise subordinate certification authority (CA) configured for key archival. Three key recovery agent certificates are issued.
The CA is configured to use two recovery agents.
You need to ensure that all of the recovery agent certificates can be used to recover all new private keys.
What should you do()
You have a Windows Server 2008 R2 Hyper-V server. You take periodic snapshots of your virtual
machines (VMs) when the VMs are not running. You delete several snapshots from the snapshot tree of a VM. The .avhd files that are associated with the deleted snapshots are not deleted from the volume where the VHD files are stored. You need to ensure that the .avhd files are deleted.
What should you do?()
You are designing a top-level OU structure to meet the business and technical requirements.
Which top-evel OU or OUs should you use? ()
You have a computer that runs Windows 7. The computer is in a workgroup. You need to ensure that youcan decrypt Encrypting File System (EFS) files on the computer if you forget your password.
What are two possible ways to achieve this goal?()
You have a single Active Directory directory service forest with one domain. You have an existing top-level organizational unit (OU) named Sales. You are planning to create a new top-level OU named Training. The Sales and Training OUs must have the same security and auditing settings. You need to identify the security permissions and audit settings for the Sales OU so that you can delegate the same permissions for the Training OU.
What should you do first?()
You work as a senior administrator at ABC.com. The ABC.com network consists of a single domain named ABC.com. All servers on the ABC.com network have Windows Server 2012 R2 installed, and all workstations have Windows 8 installed. You are running a training exercise for junior administrators.You are currently discussing the Always Offline Mode.
Which of the following is TRUE with regards to the Always Offline Mode?()
You work in a company which uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. The instance has databases for a finance application and a manufacturing application. You want to put some limitation on the maximum CPU query time allowed by the applications, so you configure the Resource Governor to achieve this. But you notice that certain reports do not execute successfully any longer on the manufacturing application. You have to allow the manufacturing application to consume more CPU time, so you have to change the Resource Governor configuration.
Which Resource Governor component should you configure?()
You have two computers named Computer1 and Computer2 that run Windows 7. Computer1 has two localuser accounts named User1 and User2. On Computer1, you run Scanstate.exe /all \\server1\data \computer1. On Computer2, you run Loadstate.exe /lac:Pa$$w0rd \\server1\data\computer1. You need toensure that User1 and User2 can log on to Computer2.
What should you do on Computer2?()
You have a portable computer that runs Windows 7. You configure the computer to enter sleep mode after10 minutes of inactivity. You do not use the computer for 15 minutes and discover that the computer has notentered sleep mode. You need to identify what is preventing the computer from entering sleep mode.
What should you do?()
You have a portable computer that runs Windows XP Professional. The computer supports Advanced Configuration and Power Interface (ACPI). You need to ensure that the computer enters Sleep Mode when you close the lid of the computer.
What should you do?()

You administer a Windows 2000 Professional computer that is shared by multiple users. You receive a phone call from one of the users of the shared computer that tells you that the computer is reporting a kernel stop error. You notice that a user has tried to install video drivers that have caused the computer to become unstable. You want to ensure that users can install only the drivers that are approved by the manufacturer.
What should you do? ()
You are designing a Windows 7 deployment image.
You plan to partition the hard disk of each client computer during deployment. You need to modify the unattended answer file by using a text editor.
Where should you add the disk information?()
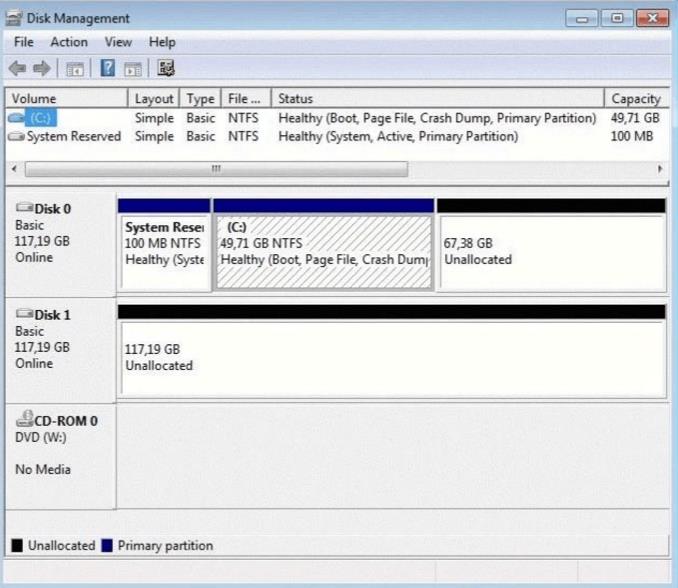
You have a computer that runs Windows 7. Your computer s disk configuration is shown in the exhibit.(Click the Exhibit button.) You need to ensure that you can create a striped volume on the computer.
What should you do?()
You are working on a very large database. You had performed a binary backup of the control file a month ago. After this you added a few tablespaces, and dropped a couple of tablespaces. This morning, due to hardware failure, you lost all your control files.
How would you recover the database from this situation?()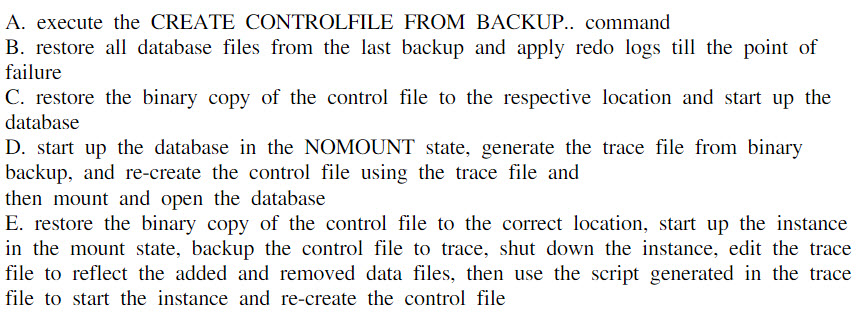
You need to identify all failed logon attempts on the domain controllers.
What should you do()
You work in a company which is named Wiikigo Corp. The company uses SQL Server 2008. You are the administrator of the company database. Now you are in charge of a SQL Server 2008 instance. There is a database named DB1 in the instance. In the database, a small percentage of data is modified everyday. Ever day in the morning, you have to create a read-only copy of the database for reporting purposes and make sure that you use as little disk space as possible.
In the options below, which strategy should you use?()
You have very few Cisco 7920 wireless IP phones on your network, but lots of wireless laptops. You want toincrease the bandwidth available for the laptops by decreasing the bandwidth reserved for the Cisco 7920phones.
What is the lowest percentage of voice-allocated bandwidth you can select on the WLANcontroller?()
You have very few Cisco 7920 wireless IP phones on your network, but lots of wireless laptops.You want to increase the bandwidth available for the laptops by decreasing the bandwidth reserved forthe Cisco 7920 phones.
What is the lowest percentage of voice-allocated bandwidth you can select ontheWLAN controller?()
You have very few cisco 7920 wireless ip phones on your network, but lots of wireless laptops. You want to increase the bandwidth available for the laptops by decreasing the bandwidth
reserved for the cisco 7920 phones.
What is the lowest percentage of voice-allocated bandwidth you can select on the wlan controller?()
You have a very few Cisco 7920 wireless IP phones on your network, but lots of wireless laptops.You want to increase the bandwidth available for the laptops by decreasing the bandwidth reserved for the Cisco 7920 phones.
What is the lowest percentage of voice-allocated bandwidthyou can select on the WLAN controller?()
You have very few Cisco 7920 wireless IP phones on your network, but lots of wireless laptops. Youwant to increase the bandwidth available for the laptops by decreasing the bandwidth reserved forthe Cisco 7920 phones.
What is the lowest percentage of voice-allocated bandwidth you can select onthe WLAN controller?()
You just completed a manual open database backup. However there seems to be a problem with the database performance. You discover that the database is generating many log switches and the LGWR is consuming lots of CPU time. You have an idea of what the problem is and you begin looking at the information in V$BACKUP and in V$DATAFILE_HEADER.
What do you suspect is the problem?()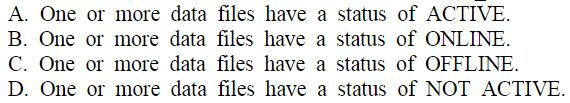
A co-worker is unable to invite you to a Microsoft Windows Meeting Space meeting. You need to receive an invite to the meeting.
What should you do?()
You are planning a Windows 7 deployment infrastructure for a new company.
You have the following requirements:
Three domains
10,000 client computers No user interaction
You need to recommend a deployment infrastructure.
What should you recommend?()
You are the administrator of Red Lington Enterprises. You want to upgrade 125 computers from Windows NT Workstation 4.0 to Windows 2000 Professional. You create an unattend.txt file by using the setup manager.
You copy the file to a floppy disk. You then start the installation on a computer in the test lab using the Windows 2000 Professional CD-ROM. After the computer starts you insert the floppy disk. Even though you set the user interaction level to full-unattended mode you are prompted for all the configuration parameters. You want to ensure that the unattended installation does not prompt you for input.
What should you do? ()
You add an Online Responder to an Online Responder Array.
You need to ensure that the new Online Responder resolves synchronization conflicts for all members of the Array.
What should you do()
You are a systems administrator responsible for configuring a Windows Server 2008 SMTP server. Yourorganization is currently using the default SMTP virtual server for sending order notifications from a single Web application called ContosoOrderManagement. Recently, you have noticed that a largenumber of messages have been sent to the SMTP virtual server from other computers and users.
Which two methods can you use to prevent unauthorized access to the SMTP server?()
You have a computer that runs Windows XP Professional. You download new video card driver from the Internet, and then install the driver. You restart the computer. You discover that the newly loaded video driver is named VgaSave.
You need to restore the previous version of the video card driver.What should you do?()
You are the administrator of your company’s network. You attempt to install a printer driver on a Windows 2000 computer for a user named Linda.
You receive the following error message: "Error 11-Cannot install printer driver."
The driver was originally downloaded from the printer manufacturer’s Web site. You have successfully used the driver in the past on their Windows 2000 Professional computers.
You want to configure Linda’s computer to check for driver integrity and to allow you to install this printer driver.
What should you do? ()
You are the administrator of ExamSheet.net's network.
You attempt to install a video driver on a Windows 2000 Professional computer. You receive the following error message: "Error 11 - Cannot install video driver."
The driver was originally downloaded from the video card manufacturer's Web site. You have successfully used the driver in the past on other Windows 2000 Professional computers. You want to configure the Windows 2000 Professional computer to check for driver integrity and to allow you to install this video driver. What should you do? ()
免费的网站请分享给朋友吧